Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
Account & Network Integrity Inspection examines how identities, permissions, and data flows interact under defined policies. The approach emphasizes precise access controls, continuous risk scoring, and anomaly detection across identities and network traffic. It considers enforcement through network rules, auditing configurations, and disciplined change control. By synthesizing insights from mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, and Njgcrby, it frames a rigorous, evidence-driven governance model that invites further scrutiny and practical evaluation.
What Is Account & Network Integrity Inspection?
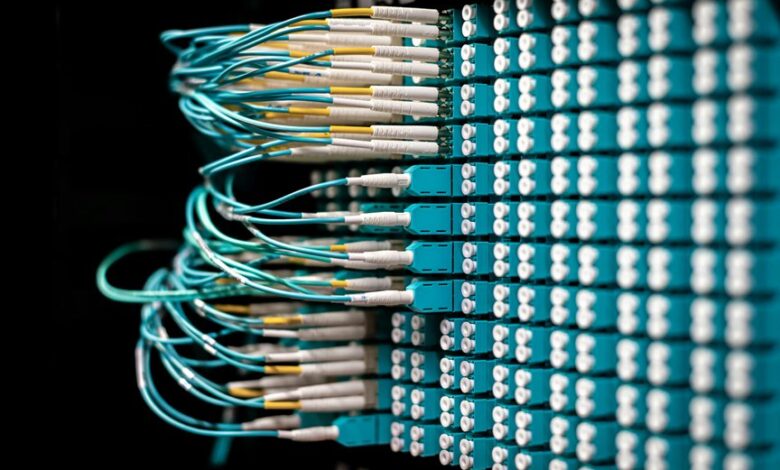
Account and network integrity inspection refers to the systematic evaluation of a system’s authentication, authorization, data flows, and communications to verify that all components operate securely and as intended.
The process emphasizes identity governance, precise access policies, and continuous risk scoring.
It aligns with network enforcement, auditing configurations, and disciplined change control to ensure resilient, compliant, and freedom-supporting operational integrity.
Detecting Anomalies Across Identities and Flows
The analysis remains objective, highlighting subtle patterns and shifts in system behavior.
Attention to identity drift clarifies longitudinal trends, while monitoring anomalous flows reveals friction points.
Vigilance ensures timely detection and resilient, freedom-supporting security postures.
Enforcing Policies: Access, Permissions, and Network Rules
Enforcing policies surrounding access, permissions, and network rules requires a precise, evidence-driven approach to ensure consistent governance across systems.
The analysis emphasizes identity governance, role-based access controls, and continuous verification, while acknowledging network segmentation as a defensive construct.
Potential pitfalls and edge cases are mapped, guiding proactive risk mitigation; clarity and auditable decisions sustain freedom through disciplined, transparent policy enforcement.
Tools, Metrics, and Best Practices for Rapid Response
Rapid response hinges on a structured toolkit: precise tools, robust metrics, and disciplined practices that collectively shorten detection-to-action timelines. The approach emphasizes anomaly detection as an early warning signal and supports decisive mitigation through codified policy enforcement.
Analysts sustain vigilance by standardized playbooks, cross-domain telemetry, and rapid containment steps, ensuring transparent accountability while preserving operational freedom and minimizing collateral impact.
Conclusion
Account and network integrity inspection stands as a meticulous custodian, parsing every credential and connection with clinical precision. It translates complex flows into transparent risk signals, turning ambiguity into measurable vigilance. By codifying access, permissions, and network rules, it threads architecture with accountability, like a loom weaving secure patterns from disparate strands. In this disciplined gaze, anomalies reveal themselves as tremors before storms, guiding proactive governance and rapid, evidence-driven responses that durable systems rely upon.