Inspect Mixed Data Entries and Call Records – 111.90.1502, 1111.9050.204, 1164.68.127.15, 147.50.148.236, 1839.6370.1637, 192.168.1.18090, 512-410-7883, 720-902-8551, 787-332-8548, 787-434-8006
Mixed data entries and call records span formats that challenge direct interpretation. From IP-like strings to phone numbers, each datum requires normalization, validation, and contextual tagging. Analysts must map identifiers to usage patterns, cross-check timestamps, and assess consistency across sources. A disciplined workflow reveals normal versus anomalous activity, informing alerts and traceability. The approach balances rigor with practical workflows, yet unresolved ambiguities in edge cases point to further refinement and ongoing scrutiny.
What Mixed Data and Call Records Reveal About Activity
Mixed data entries and call records offer a granular view of activity patterns, revealing not only when interactions occurred but also the contexts and frequencies that underlie them.
The analysis isolates mixed data signals and call records to map behavior, identify anomalies, and delineate patterns.
This method supports anomaly detection, emphasizing systematic, evidence-based interpretation of activity patterns with clarity.
How to Normalize and Validate Diverse Identifiers
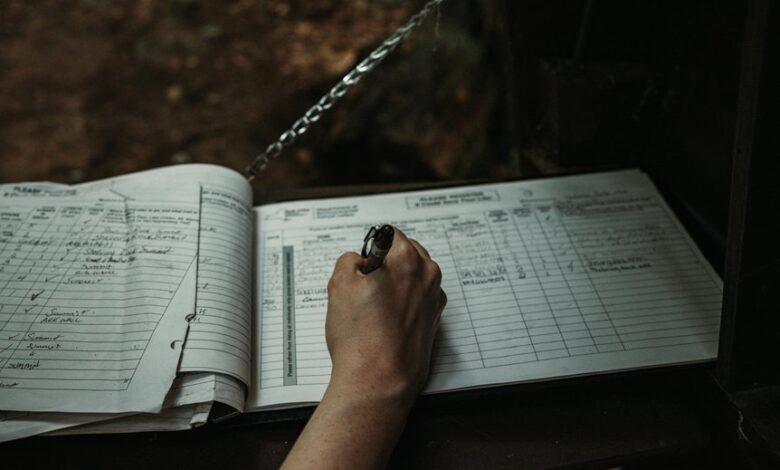
Normalization and validation of diverse identifiers are essential to ensure consistent interpretation across systems, datasets, and processes. The analysis outlines a disciplined workflow: catalog formats, apply canonical forms, and enforce validation rules before integration. Data normalization aligns structures; identifier validation confirms syntax, length, and checksum when applicable. This rigorous approach reduces ambiguity, enhances interoperability, and supports reliable downstream analytics and decision-making.
Cross-Referencing Data for Anomaly Detection
Cross-referencing data across disparate sources is a systematic approach to reveal anomalies that single datasets may conceal. It assesses consistency and corroborates signals across networks, logs, and records. Analysts identify anomaly indicators by comparing formats, timestamps, and usage patterns. This method reinforces identifier integrity, highlights outliers, and strengthens confidence in anomalous findings while preserving traceability and reproducibility.
Practical Workflow: From Logs to Insights and Alerts
From the prior focus on cross-referencing data across disparate sources, the practical workflow moves from validating signal integrity to translating that validation into actionable insights and timely alerts.
The process embraces data normalization to unify heterogeneous entries, enabling consistent analysis; anomaly detection then highlights deviations.
Clear thresholds and concise dashboards transform logs into targeted notifications, supporting proactive investigation and disciplined, freedom-oriented decision-making.
Conclusion
In a disciplined, third-person cadence, the analysis closes by noting coincidence as a quiet thread linking disparate records: a reused pattern here, a familiar format there, suggesting underlying processes rather than random chance. The methodical cross-checking of timestamps, formats, and usage bursts reveals a coherent activity map where anomalies emerge as deviations from expected coincidences. The result: a reproducible, alert-ready framework that treats each data point as a potential lead in a larger, interconnected narrative.




