Incoming Communication Record Audit – anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh
The incoming communication record audit brings together anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, and Doumneh to define scope, methodologies, and governance. The goal is precise provenance, privacy controls, and auditable logs across cross-border contexts. Stakeholders will map taxonomy to standardized records, assess retention timelines, and establish escalation paths. The approach remains disciplined and transparent, but questions about implementation and risk still demand careful alignment before proceeding.
How to Define an Incoming Communication Record Audit Scope
Defining the scope of an incoming communication record audit entails establishing clear boundaries that specify which communications, timeframes, systems, and data sources will be examined.
The scope delineates data preservation, access rights, and cross-border considerations while mapping responsibilities.
It addresses compliance challenges and privacy controls, ensuring evaluators focus on relevant artifacts, exclude extraneous material, and uphold transparent, auditable procedures throughout the review process.
Key Audit Methodologies for Inbound Messages
The framework emphasizes structured sampling, traceable provenance, and objective criteria.
It maps inbound taxonomy to standardized records, defines audit milestones, and records deviations with justification.
Findings are documented, reproducible, and actionable, supporting transparent governance while preserving analytical flexibility for stakeholders seeking freedom within boundaries.
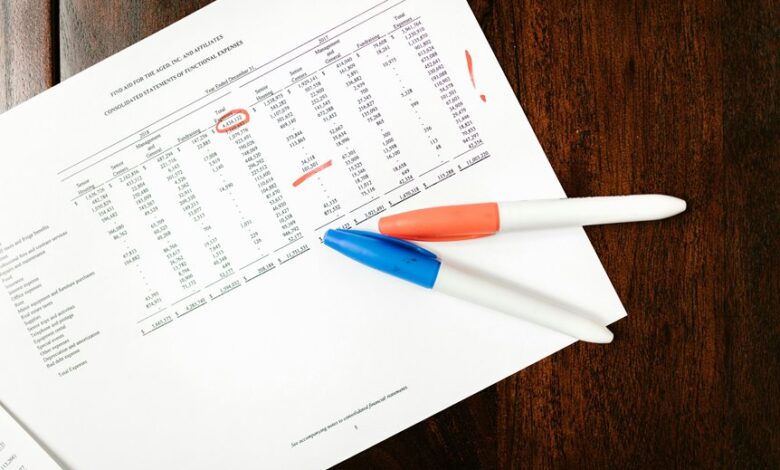
Ensuring Compliance, Privacy, and Traceability in Practice
How can organizations ensure that inbound communications are processed in a manner that simultaneously satisfies compliance requirements, protects privacy, and preserves traceability across all stages of the audit workflow? The approach emphasizes robust privacy controls, auditable access logs, and defined retention timelines. Compliance sampling validates controls, while meticulous recordkeeping supports traceability and accountability throughout processing, review, and disposition.
Practical Pitfalls and Best Practices for Fast-Paced Environments
In fast-paced environments, inbound processing must balance speed with controls established in prior discussions of compliance, privacy, and traceability. Practitioners implement lifecycle mapping to delineate stages, responsibilities, and data handling boundaries, while performing ongoing risk assessment to identify vulnerabilities.
Clear escalation, documentation, and auditing cycles mitigate drift, ensuring rapid decisions remain aligned with policy, governance, and accountability objectives.
Conclusion
The meticulous, methodical monitor scrolls, mapping messaging metrics, maintaining meticulous provenance, and mandating measurable maintenance windows. Stakeholders steadfastly synchronize scopes, securely segment sensitive data, and strictly supervise retention timelines. Procedural prudence proliferates, preserving privacy, promoting transparent tracing, and preventing cross-border lapses. Regular risk reviews reinforce rigorous governance, rendering rapid response feasible without sacrificing standards. Clear escalation, consistent communications, and accountable documentation anchor auditable outcomes, ensuring inbound information remains integrated, incorruptible, and instructional for future iterations.