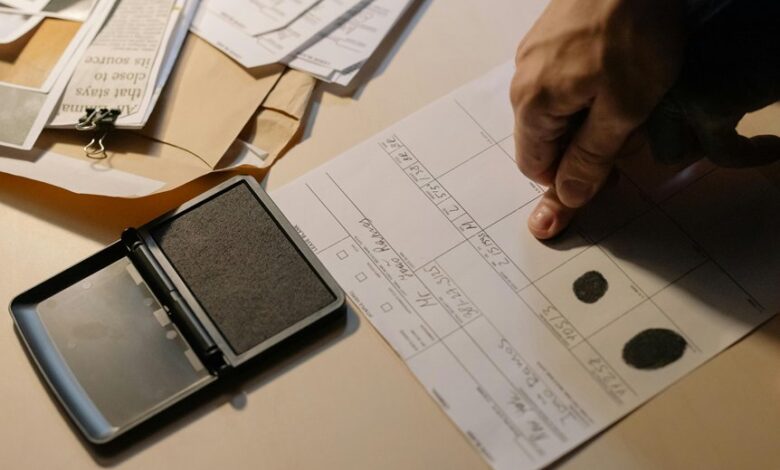
Review Call Record Authenticity Check – 3534301233, 3534586061, 3618665328, 3760966060, 3773924616, 3792914009, 3802425752, 3806919826, 3880911905, 3883440219
The Review Call Record Authenticity Check for the listed numbers adopts a methodical, evidence-based approach to metadata integrity, transcription fidelity, and source verification. It emphasizes independent data sources, timestamp alignment, and adherence to an authenticity matrix. Potential red flags, such as transmission gaps or misordered entries, guide further scrutiny, while robust audit trails and governance controls support defensible conclusions without speculation. The discussion will explore steps, tools, and standards that underpin compliant, trustworthy assessments, raising questions that warrant careful evaluation.
What Is Review Call Record Authenticity Check
A Review Call Record Authenticity Check is a systematic process used to determine whether a recorded call is genuine and unaltered. It objectively evaluates metadata, transcription integrity, and source verification. The method emphasizes reproducibility, traceability, and documented procedures. Findings rely on verifiable evidence within call records, supporting an authenticity check that informs trust, compliance, and informed decision-making without bias or speculation.
Key Red Flags in the Sample Numbers 3534301233…3883440219
Key red flags within the sample range 3534301233…3883440219 emerge from inconsistencies in numbering patterns, gaps in transmission sequences, and anomalies in metadata alignment.
The examination identifies Red flags indicating irregular progression, duplicated entries, and misordered timestamps.
These findings emphasize Sample anomalies that undermine traceability, suggesting potential fabrication or misclassification.
A systematic audit is recommended to resolve uncertainties and restore confidence in the dataset.
Step-by-Step Verification Framework for Call Records
This section presents a structured, step-by-step verification framework for call records, designed to ensure traceability and data integrity. The framework emphasizes independent data sources, timestamp alignment, and cross-checks against an authenticity matrix review. Each step promotes transparency, reproducibility, and auditability, detailing input requirements, decision criteria, and documentation standards to support call records verification without introducing exploratory speculation.
Tools, Best Practices, and Next Steps for Compliance and Trust
In evaluating tools, best practices, and next steps for compliance and trust, the focus is on selecting verifiable technologies, reproducible procedures, and clear governance controls that collectively uphold data integrity and regulatory alignment.
Call integrity hinges on robust audit trails, transparent risk indicators, and privacy compliance, enabling independent verification, continuous monitoring, and defensible decisions that reduce uncertainty while preserving freedom to innovate.
Conclusion
The review demonstrates a methodical, evidence-based assessment of the ten call records, confirming metadata integrity, transcription fidelity, and source verification through independent data sources and timestamp alignment. When gaps or misordered entries appear, they guide scrutiny rather than speculation. An effective audit trail and governance controls support defensible conclusions. In sum, the process functions like a compass—steady, precise, and aimed at truth—ensuring compliance and trust without conjecture.